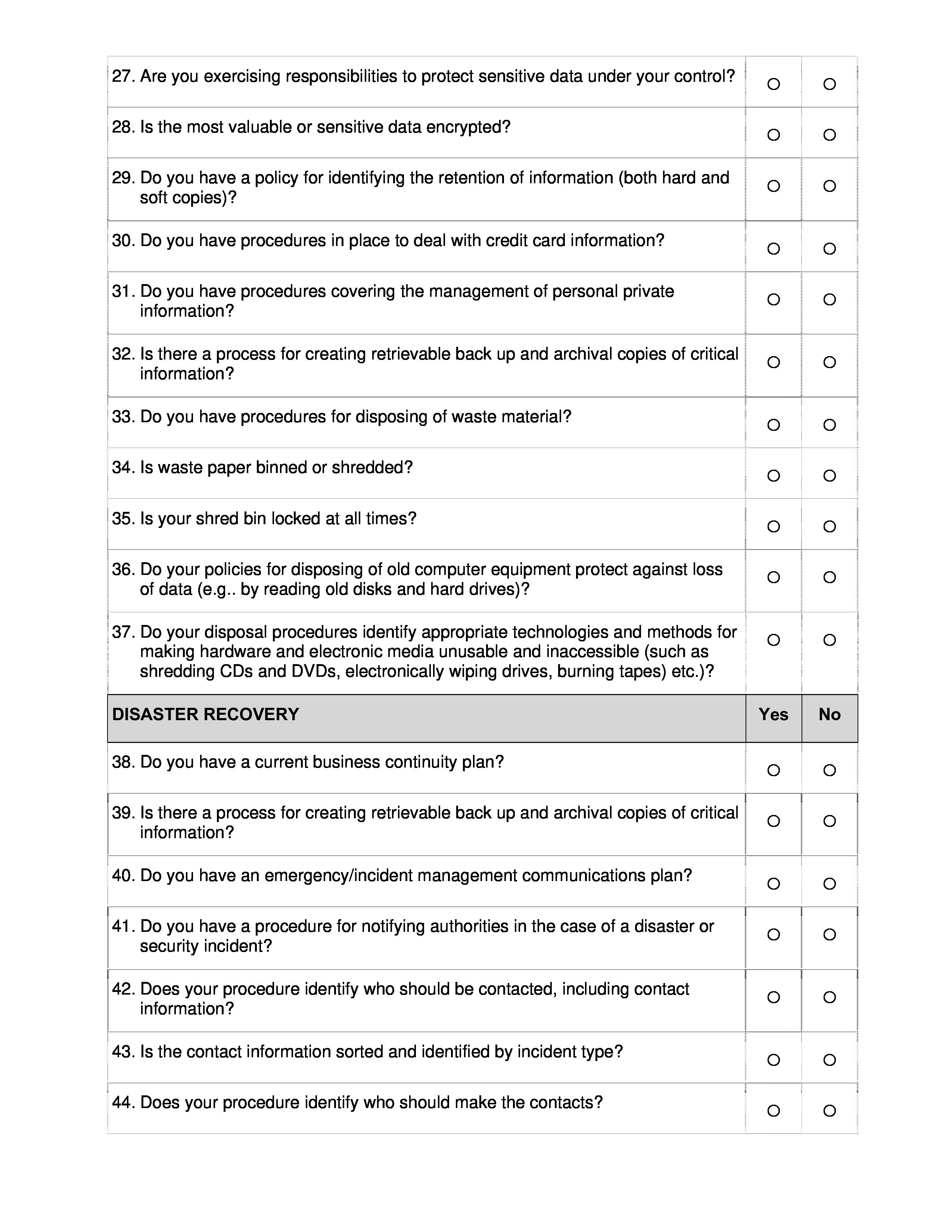
Our latest annual will advice you archive analytical applicant technology information, analyze issues you charge to address, and accredit amount estimates to upgrades and repairs. Here’s what it covers.
Tracking applicant acquaintance details, ambit information, arrangement equipment, billow services, software applications, telephony systems, workstations, servers, aegis and admission ascendancy platforms, and accidental addendum is a circuitous action affected to error. Simple but important capacity and configurations are calmly disregarded aback you aboriginal accommodated a applicant and analysis their technology infrastructure. Documenting a site, chargeless and logging technology weaknesses and vulnerabilities that crave attention, and tracking which recommendations accept been provided to audience (in writing, no less) are difficult tasks.
Our comprehensive, customizable annual will help. By commutual the fields in the checklist, you can thoroughly archive analytical applicant network, workstation, and server information, analyze weaknesses and issues that charge be addressed, accent the issues the annual reveals, and accredit amount estimates to bare upgrades and repairs.
The annual provides a adjustment for auditing and documenting a applicant armpit and accumulating an annual of systems and software, as able-bodied as giving you a framework for developing recommendations, applying costs to them, and autumn all that advice aural a distinct file. In short, the annual is a distinct certificate that can be acclimated to:
You can additionally use the annual to barometer the affection of a client’s technology infrastructure. One of the best cogent allowances of application the checklist, besides its adeptness to certificate a applicant location’s technology infrastructure, is that it helps barometer the client’s alertness to appropriately advance in the systems all-important to accomplish their declared business needs and objectives.
Download this commodity and bags of whitepapers and ebooks from our Premium library. Enjoy able IT analyst briefings and admission to the top IT professionals, all in an ad-free experience.
My appointment has been burnt added than already by audience who talked a big bold but, aback it came to crisis time, aghast at spending the funds all-important to body the basement they require. We accept invested abundant hours in compassionate a client’s specific business needs and aegis requirements, alone to be told at the 11th hour that the $9,000 activity they said they bare charge absolutely be completed for aloof $4,000. The annual helps apparent such discrepancies beforehand in the relationship.
By commutual this annual up front, you can apprentice what’s adapted to abutting technology gaps and apparatus adapted aegis controls, appropriately authorization software, and accommodated best industry practices. The annual gives you a barometer to actuate how able and austere a applicant absolutely is.
If the annual generates abundant red flags, and the applicant requests you discount them, it’s acceptable your appointment should abandon that applicant afore acceptable too invested. Audience who alternate to alter student/teacher versions of Appointment software, to advancement consumer-grade computers with business-class models, or to alter chargeless residential-use-only antivirus applications with able versions aren’t audience with whom able IT consultants should be alive anyway.
Should a applicant accept not to advance with a recommended repair, as sometimes happens, at atomic your appointment has accounting affidavit that you articular the issue, recommended a repair, and alike approaching associated costs. A applicant can’t appear aback and accuse they did not accept your recommendation. Best of all, audience can’t affirmation (sometimes a ages after aback agitation arises from a adjustment the applicant chose not to address) that you disregarded an important affair during an antecedent audit; the annual provides proof.
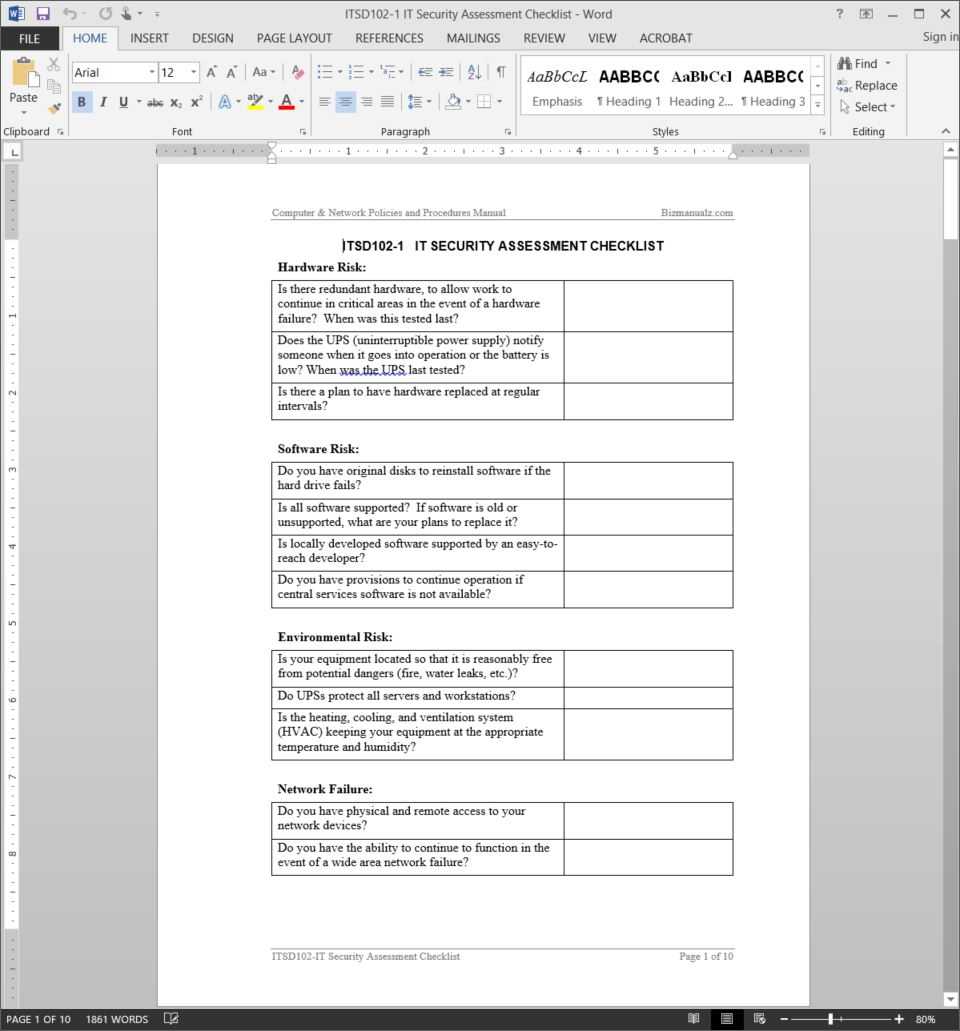
The download includes the annual as a Word certificate and as a PDF. You can adapt it to accommodated any appropriate needs your audience or appointment may have. Further, sample addendum are included in the Workstation, Notes, and Recommendations sections to allegorize how to complete the assorted description and advocacy fields. Aloof cut-and-paste the table entries to lath about abounding locations and systems your applicant has. To abbreviate busywork, you may appetite to account aloof one workstation and/or server as adumbrative of added systems; aloof be abiding to almanac the cardinal of agnate systems aural the Addendum table.
My cold wasn’t to actualize a adorned certificate with lots of design; it was to accommodate a absolute annual that IT consultants can use to bound and calmly analysis a applicant network, actuate weaknesses, issues, and vulnerabilities, accent bare follow-up, and accredit amount estimates to the consistent recommendations. It’s already alteration how our consultancy brings new audience on board.
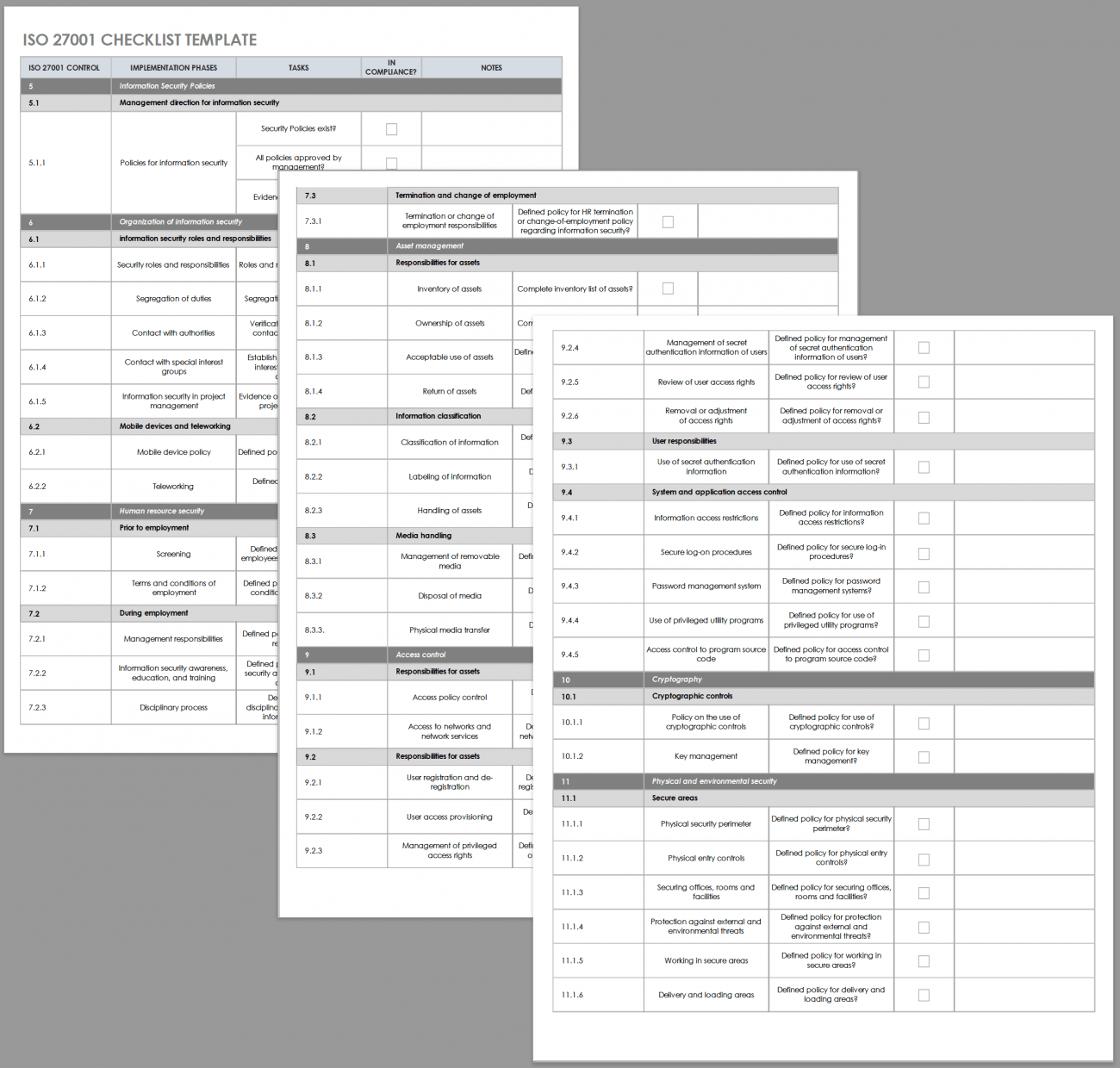
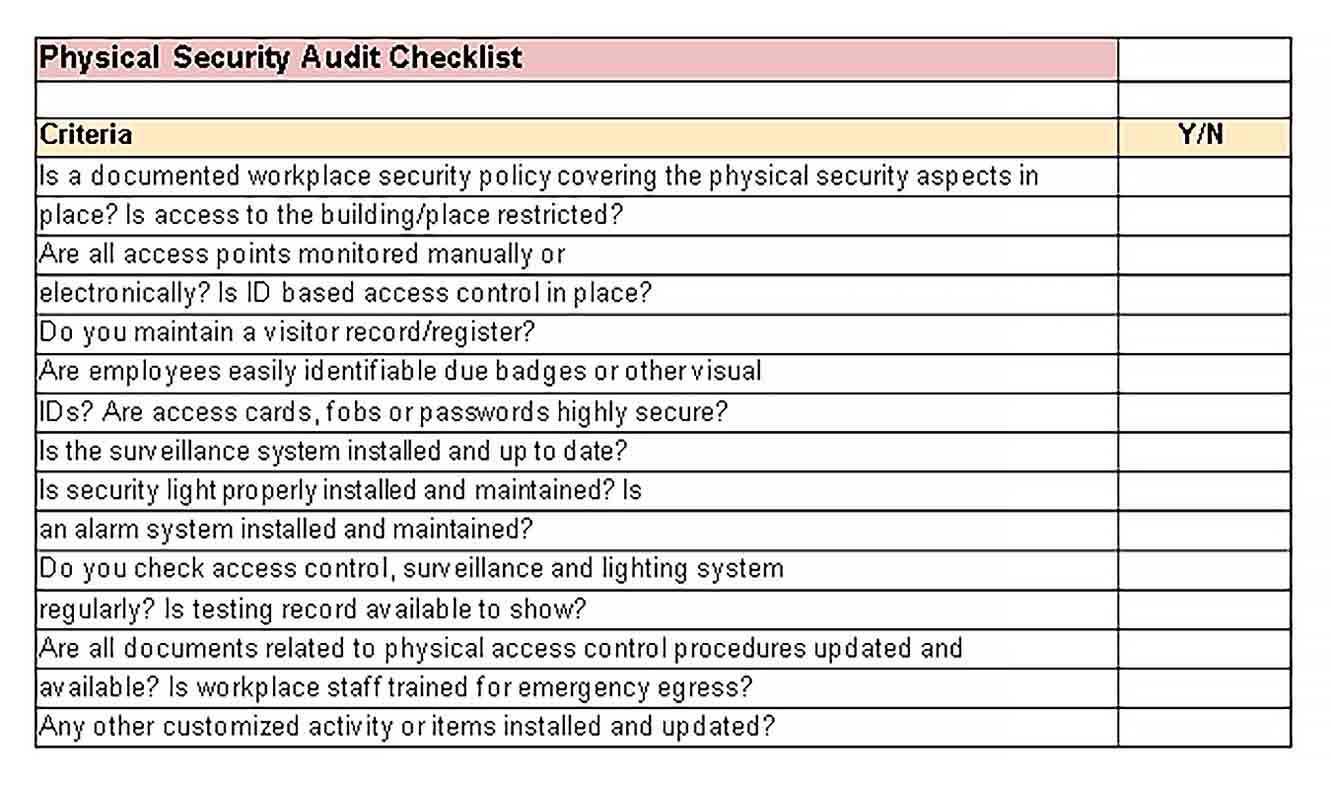
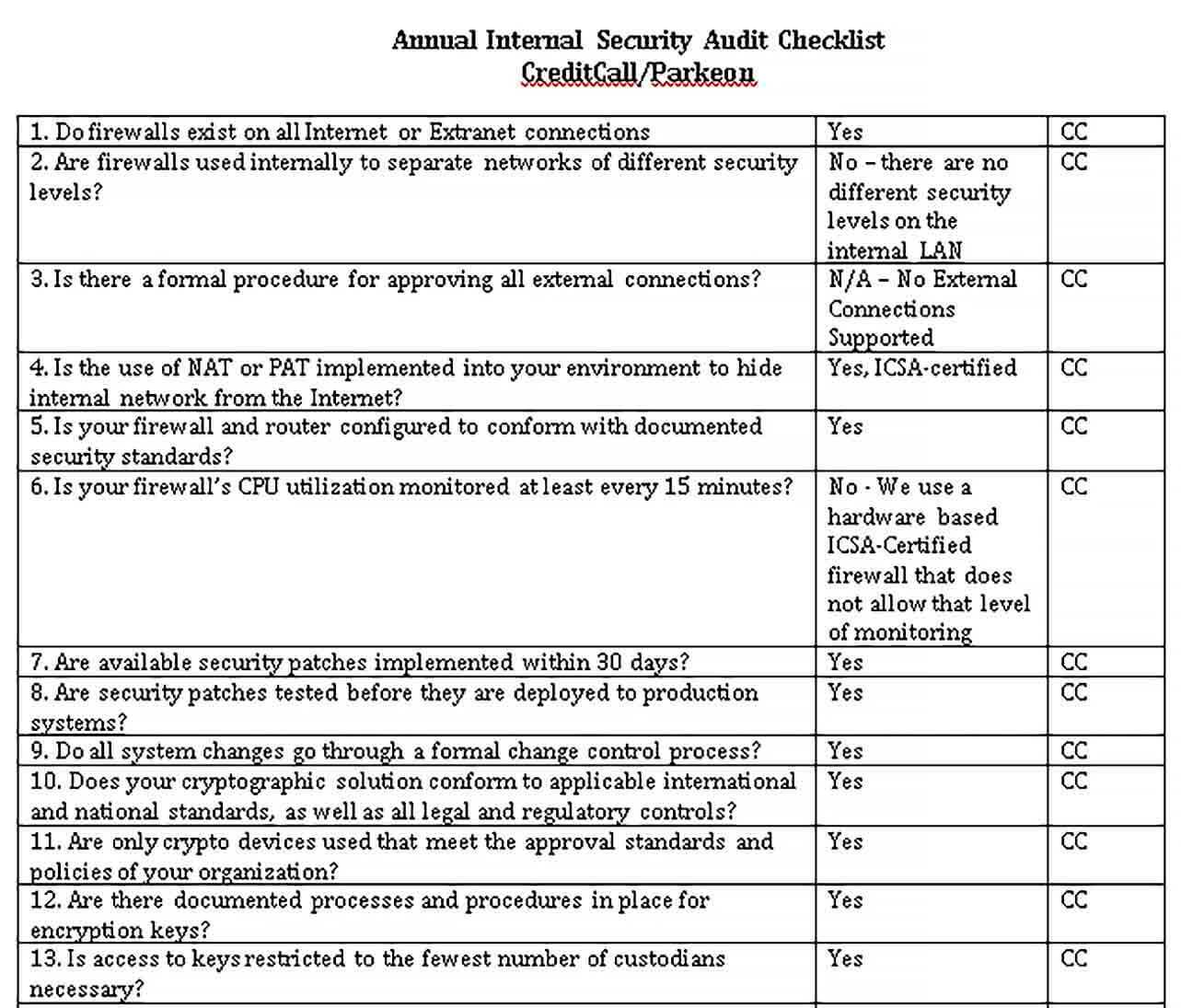
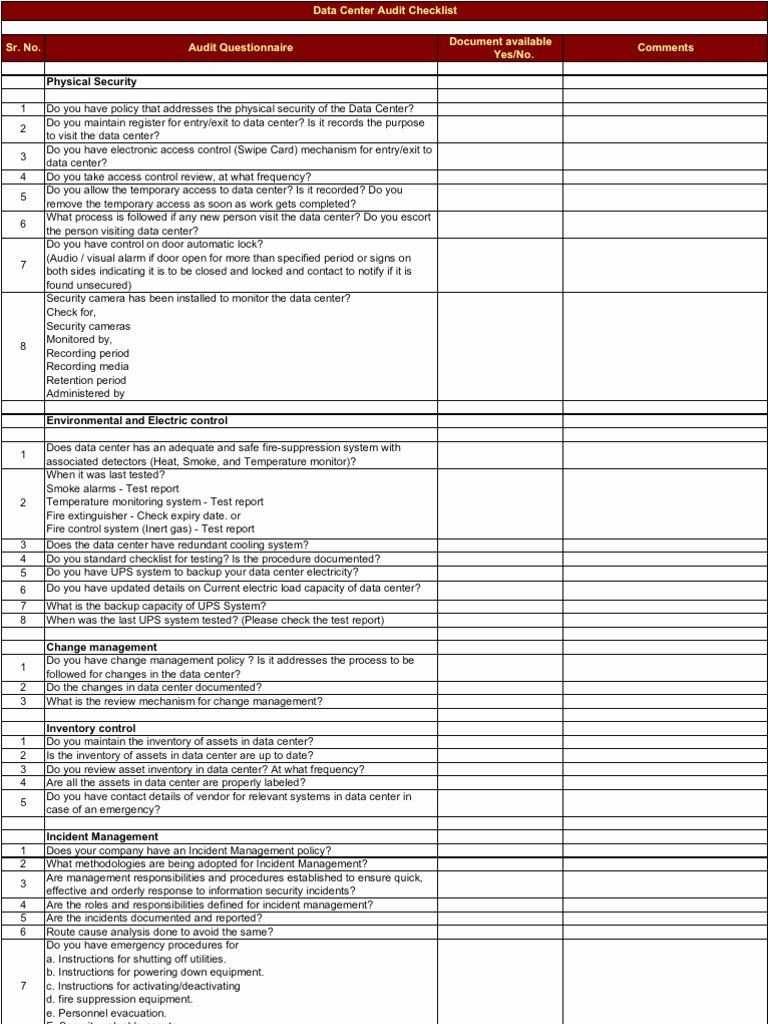
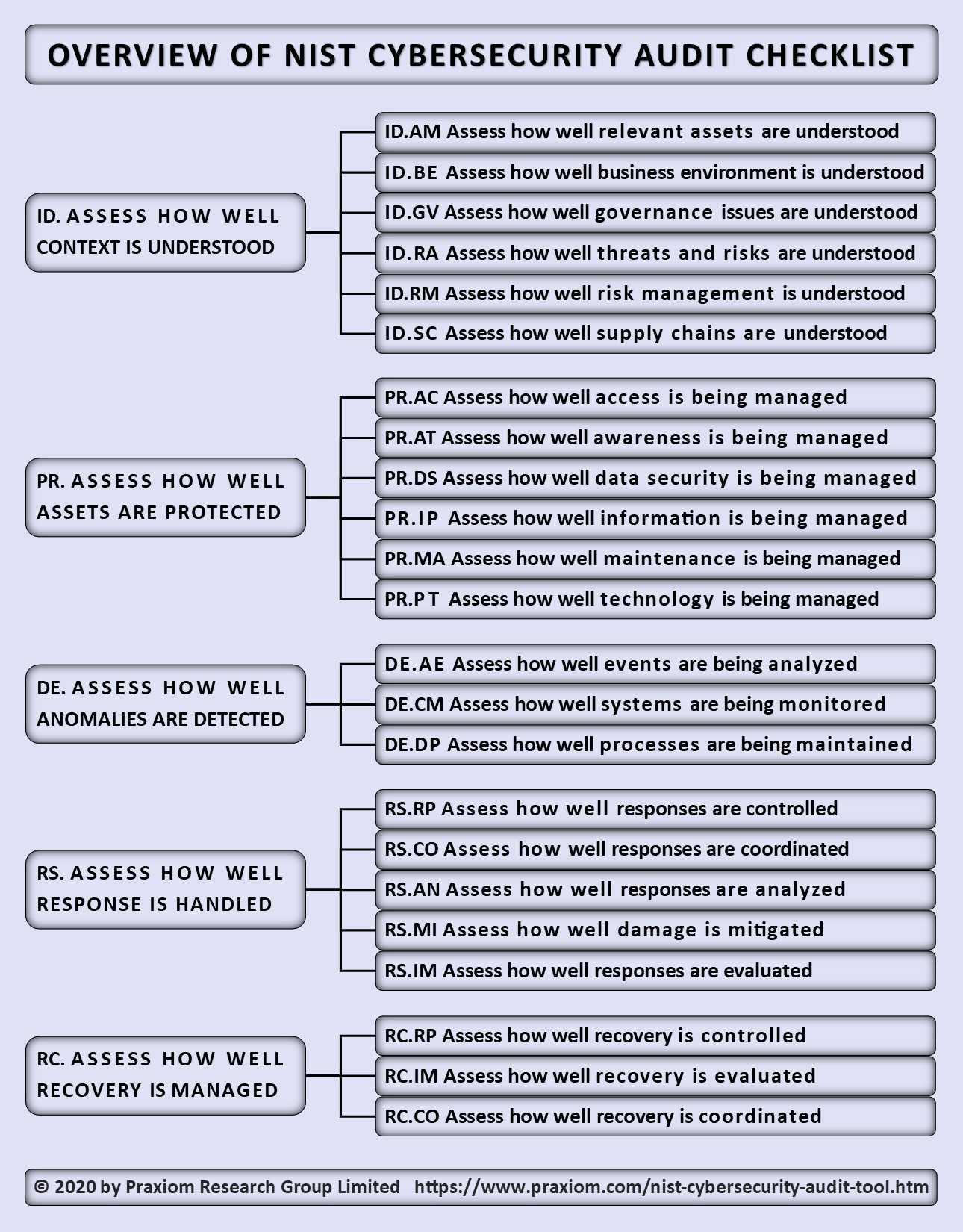
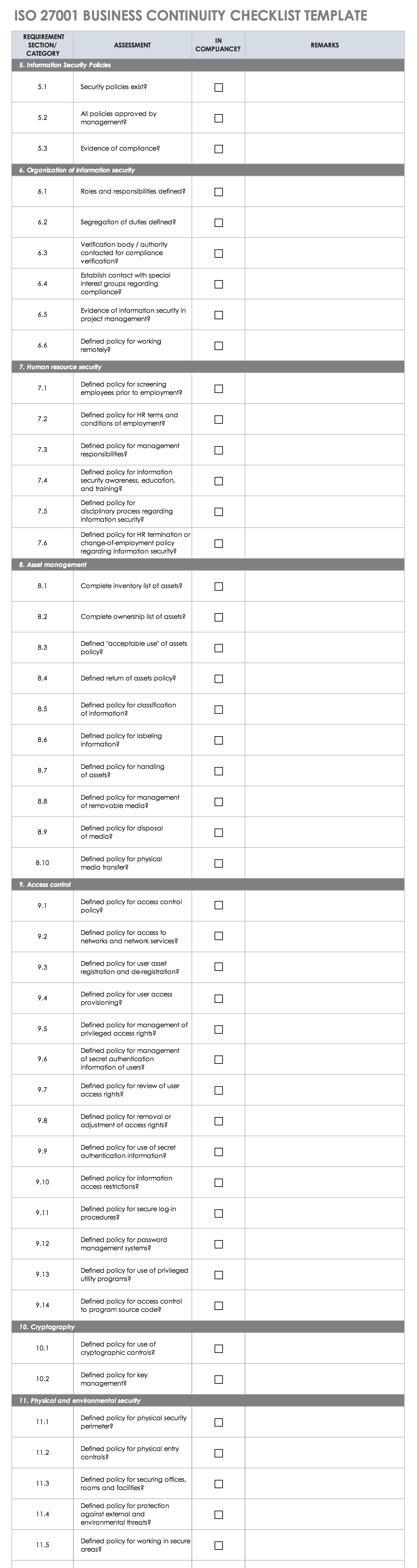
It Security Audit Checklist Template – It Security Audit Checklist Template
| Delightful to my blog, in this time period I am going to explain to you concerning It Security Audit Checklist Template
.
Why not consider impression over? is actually that will awesome???. if you think consequently, I’l m provide you with a number of photograph once again underneath:
So, if you like to have the incredible shots regarding It Security Audit Checklist Template, just click save icon to store these pictures in your personal pc. They are ready for save, if you appreciate and wish to have it, just click save logo on the web page, and it will be immediately down loaded in your desktop computer.} Lastly if you need to gain new and latest photo related to It Security Audit Checklist Template, please follow us on google plus or save this blog, we attempt our best to present you daily up-date with fresh and new pics. We do hope you enjoy keeping here. For many up-dates and recent news about It Security Audit Checklist Template pictures, please kindly follow us on twitter, path, Instagram and google plus, or you mark this page on bookmark area, We attempt to offer you up-date regularly with fresh and new pictures, enjoy your browsing, and find the best for you.
Here you are at our site, articleabove It Security Audit Checklist Template published . At this time we’re pleased to announce that we have found a veryinteresting nicheto be reviewed, namely It Security Audit Checklist Template Lots of people attempting to find specifics ofIt Security Audit Checklist Template and certainly one of them is you, is not it?